Serenicity Control
Taking back control of your information system has never been easier.
Data visualization reimagined
Find simple and powerful features, all in one interface.
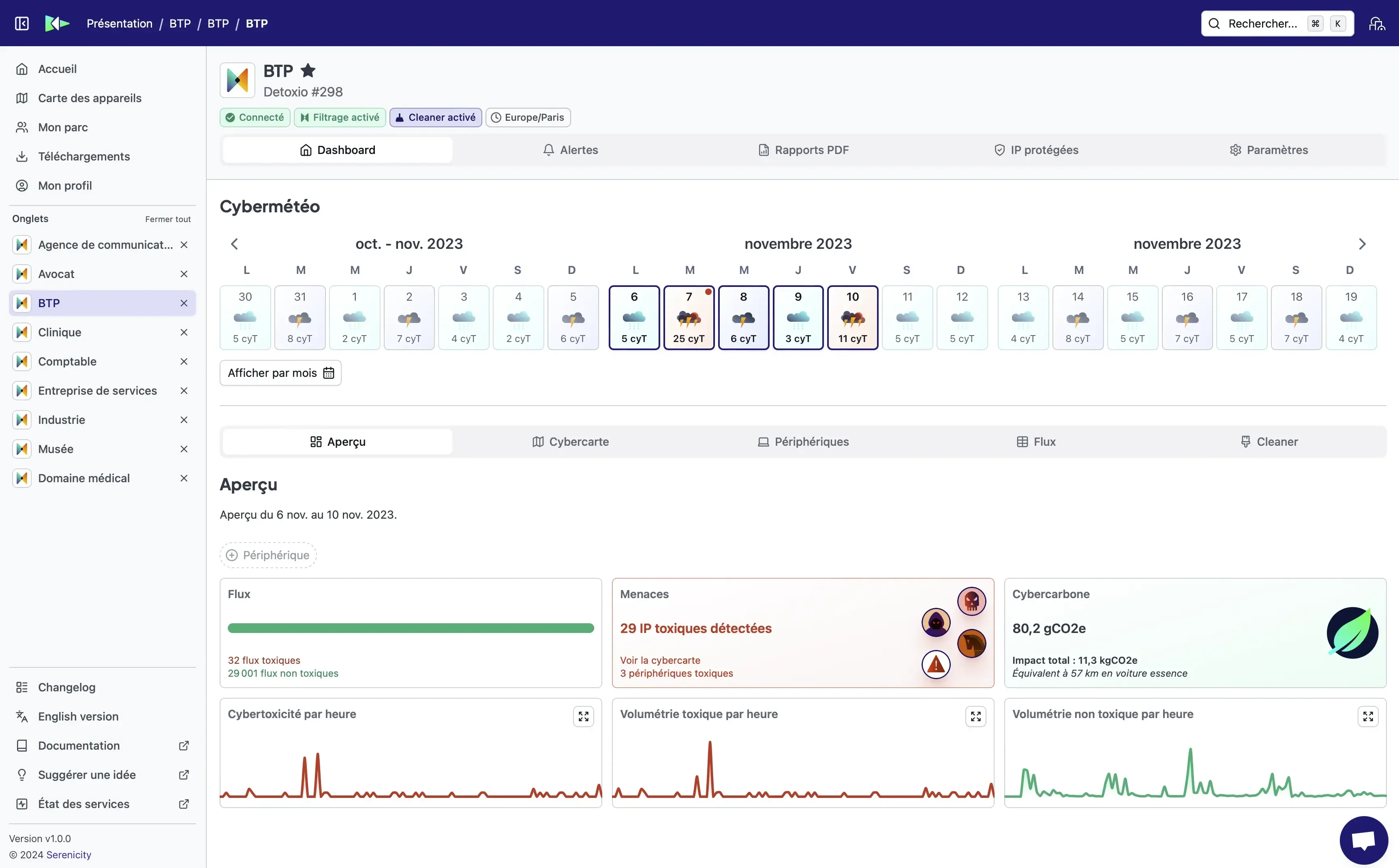
Cyberweather
Give a simple visualization on the IT risk that weighs on your network.
Alerts
Set up alerts to react quickly when an attack is detected.
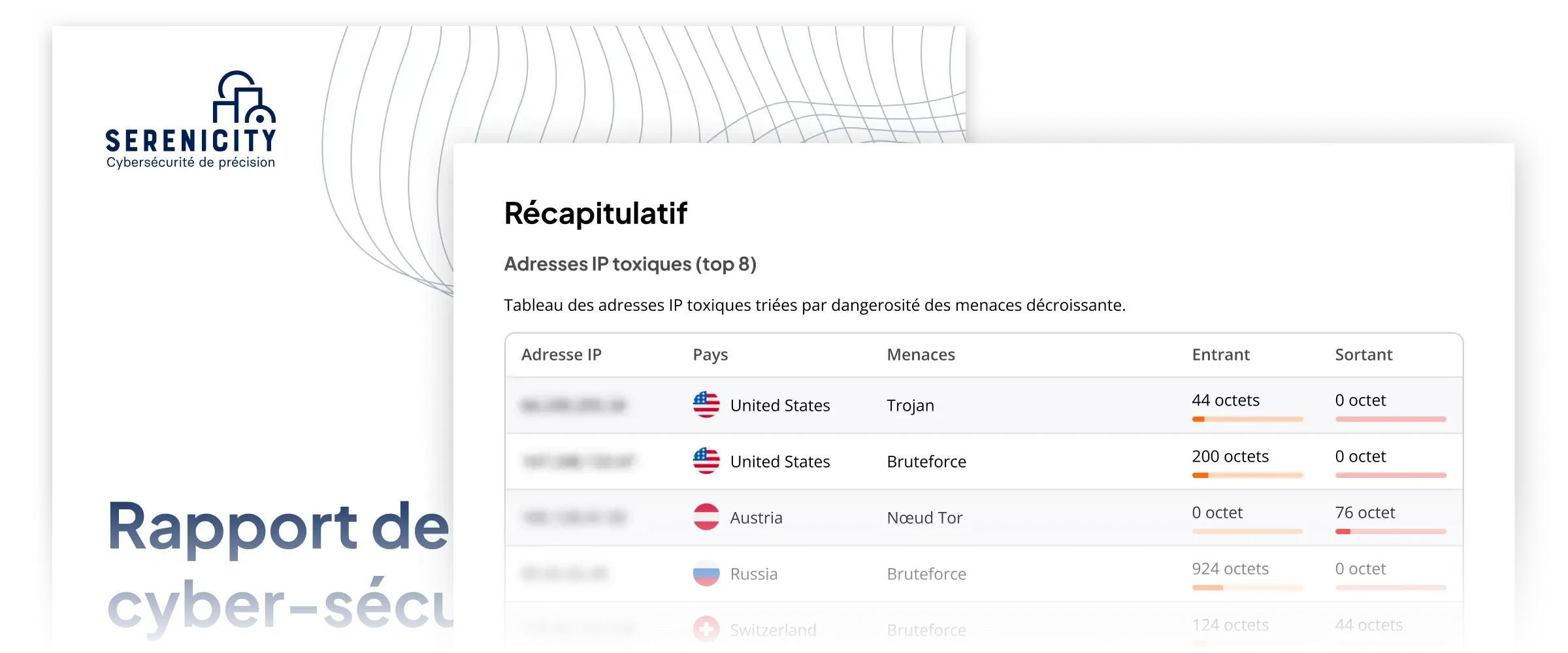
PDF report
Generate simple, easy-to-understand PDF reports with just a few clicks.
A intuitive interface
Serenicity Control is easy to use and can easily read the data provided by Detoxio and Cymealog.
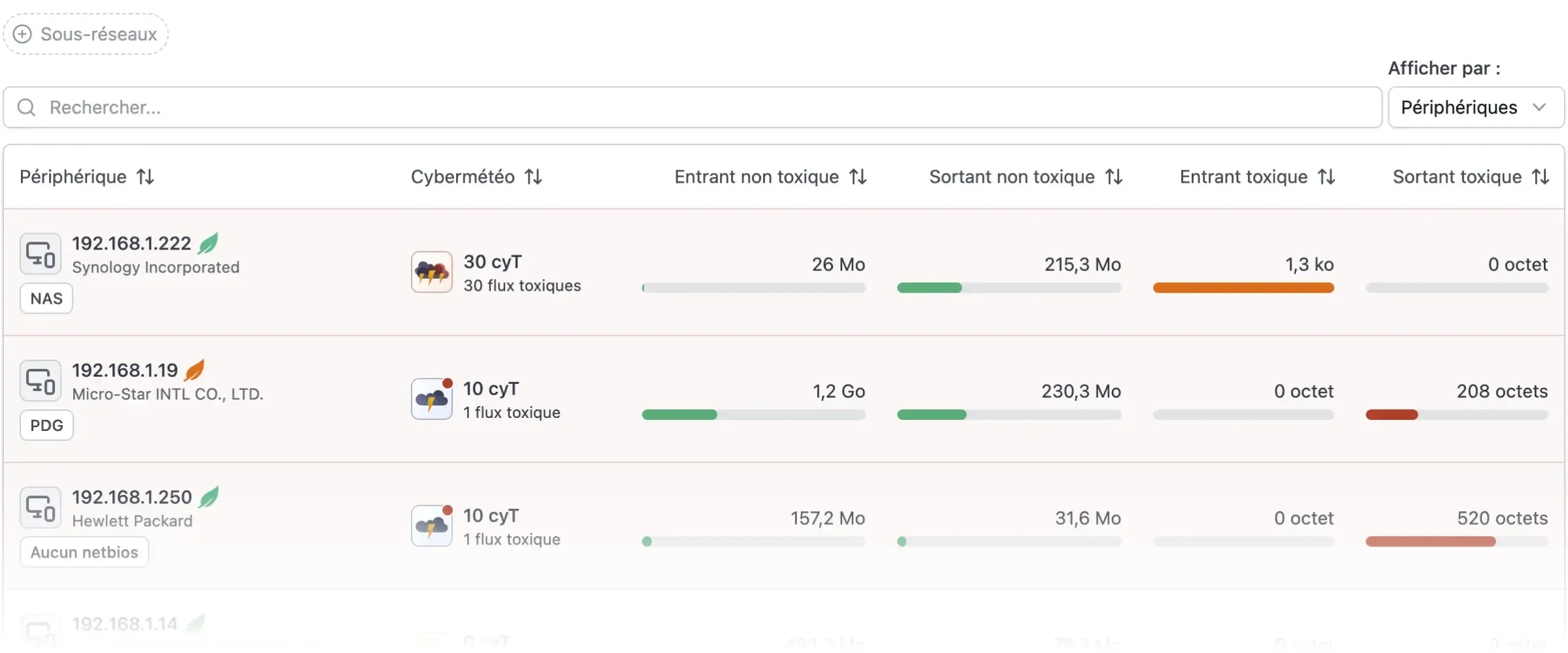
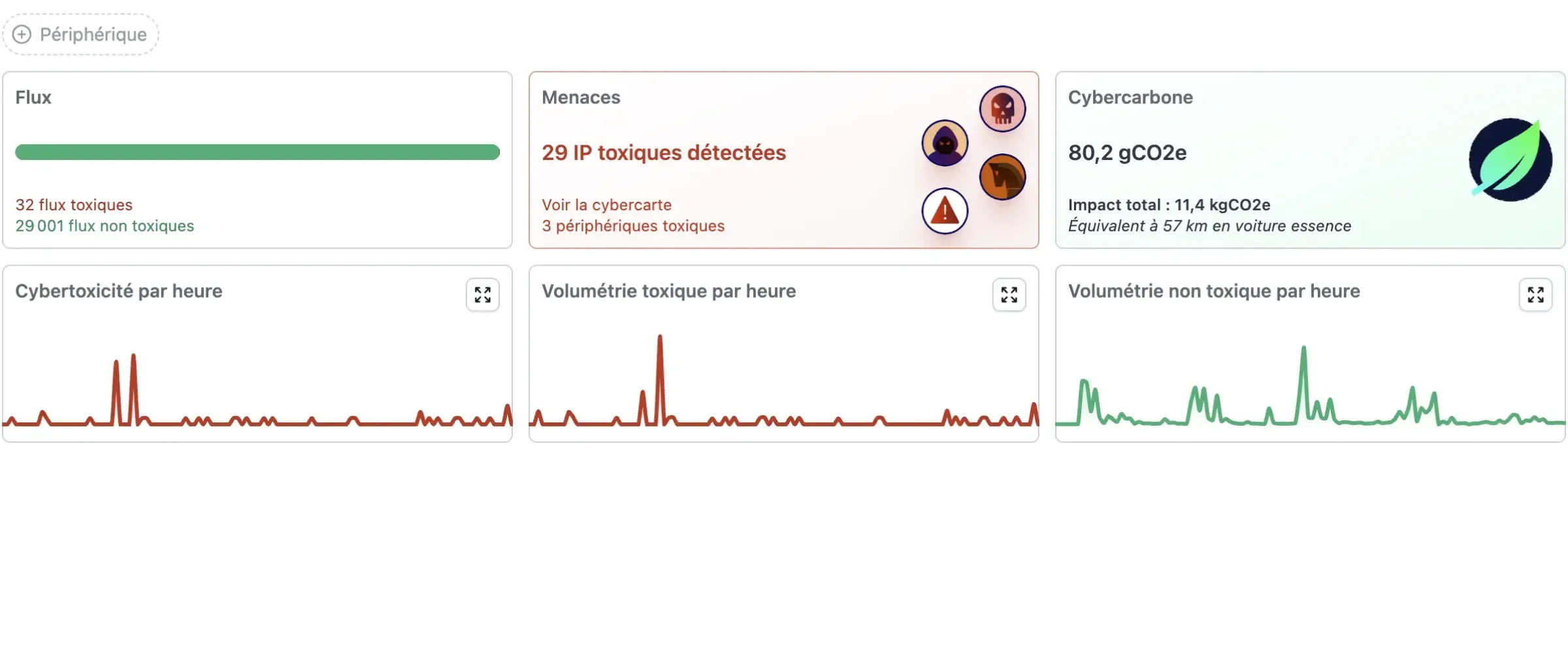
Dashboard
Get a quick overview of the status of your information system.
Make the invisible visible
Discover the origin of the threats and the attacking IPs blocked thanks to the cybermaps.
Keep an eye on your cyber security
Simplify your IT security management with Control, the next generation dashboard that gives you effective control over your network.
Alerts
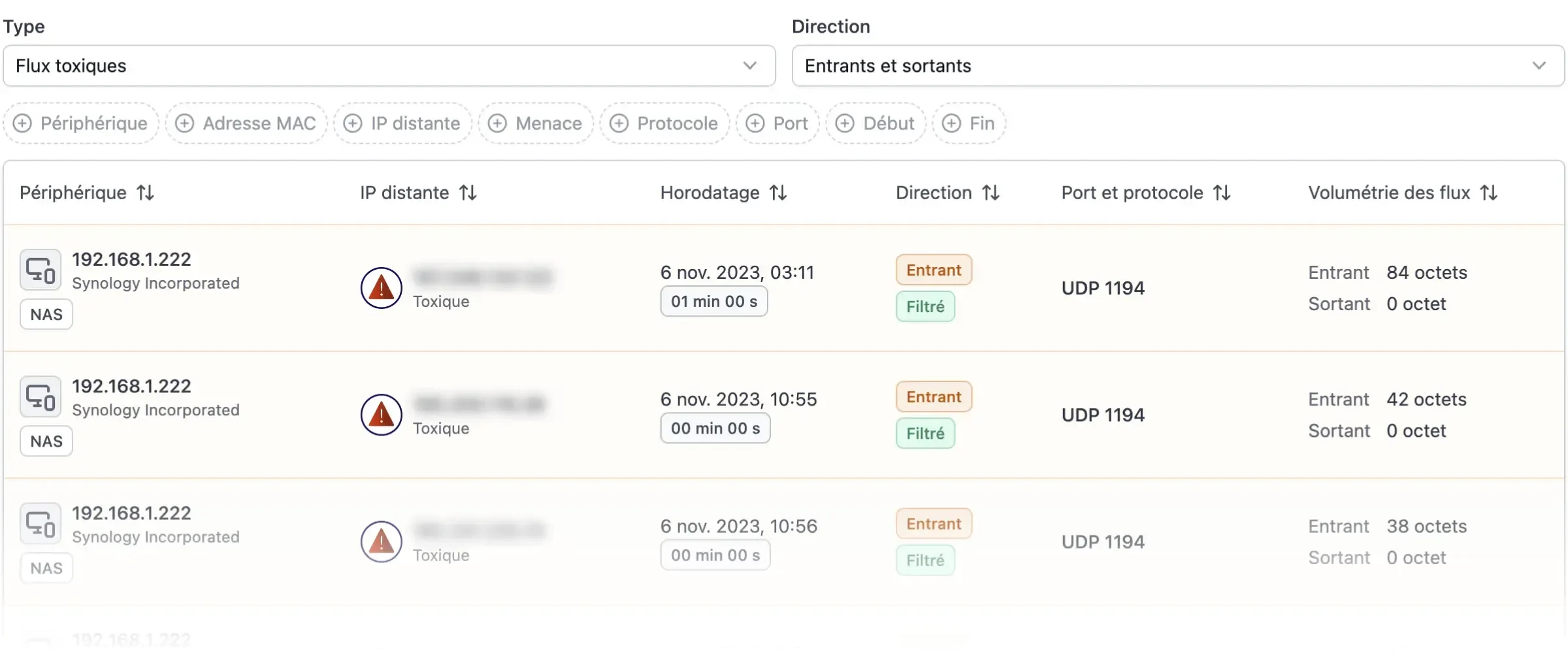
Simply set up your alerts to be notified when toxic flows are detected on your network.
Interactive
Visualizing your toxic flows on a map lets you quickly understand the origin of threats.
Secure
Connection to Control is enforced with strong authentication. Receive your code by email, SMS or via your favorite MFA application.
Frequent updates
Control is frequently enriched with new features. No manual update is required, just refresh your browser.
PDF reports
PDF report generation lets you easily export the status of your information system.
API
Control provides simplified API access so you can retrieve your data as easily as possible.
Serenicity Cerbère
The Serenicity Cerbère database is constantly updated with the latest indicators of compromise based on our patented technologies and our agreements with the authorities.
Integrated with solutions
Serenicity Cerbère is continuously updated with Detoxio and Cymealog to quickly detect and block suspicious activity and malicious behaviour before it causes damage.
Connected with our partners
Our agreements with the authorities and our private partners guarantee a constant flow of intelligence on the latest and most advanced threats.
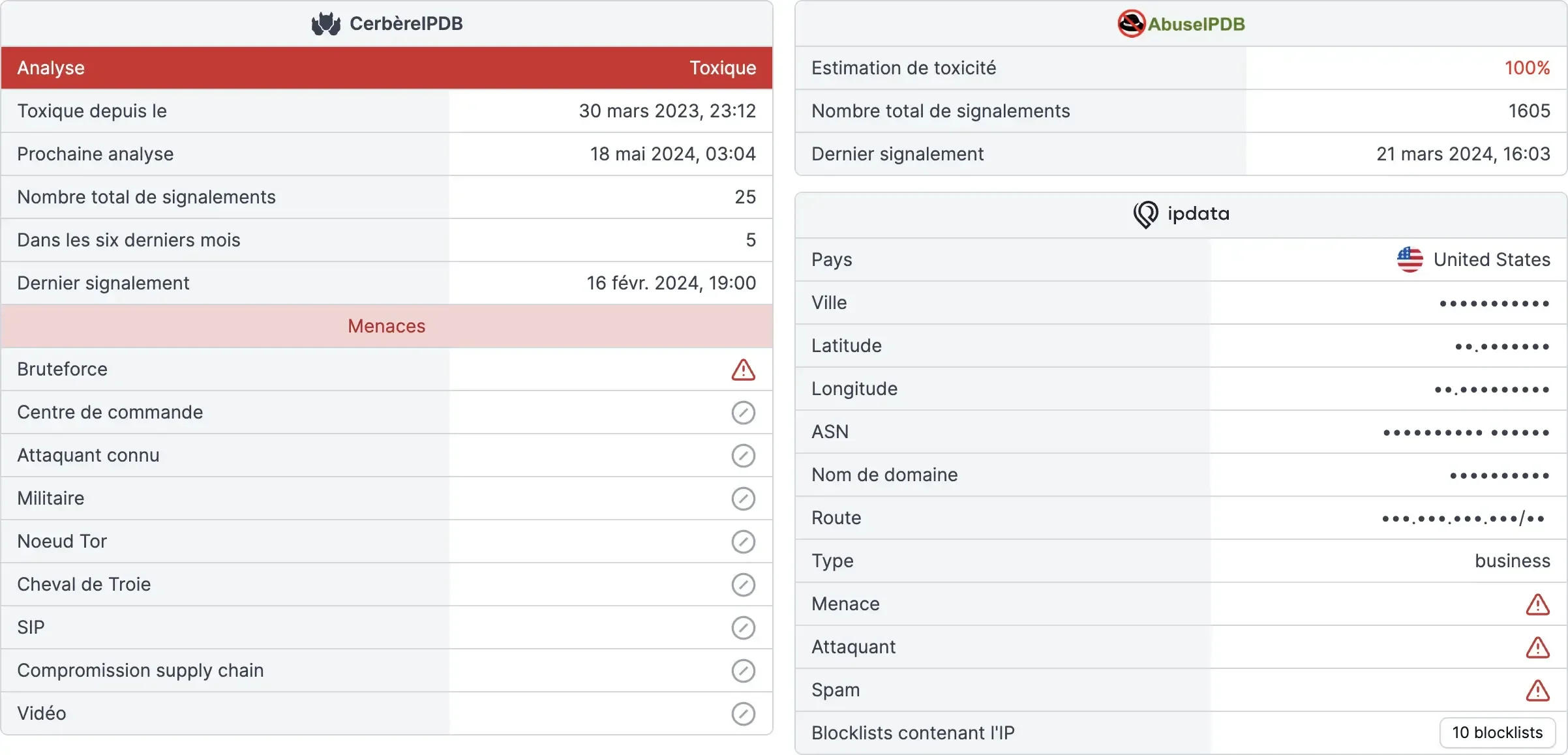
Precise qualification
Serenicity Cerbère provides accurate and reliable information on threats in order to protect your information system: location, typology, host, etc.
Behavioural analysis
Indicators are updated in real time based on Internet threat activity to provide comprehensive and proactive protection.
Sovereignty by design
Our solutions designed and developed in France are hosted in Europe.
Our products ensure the security of your data, particularly with regard to RGPD requirements and extra-territorial laws.